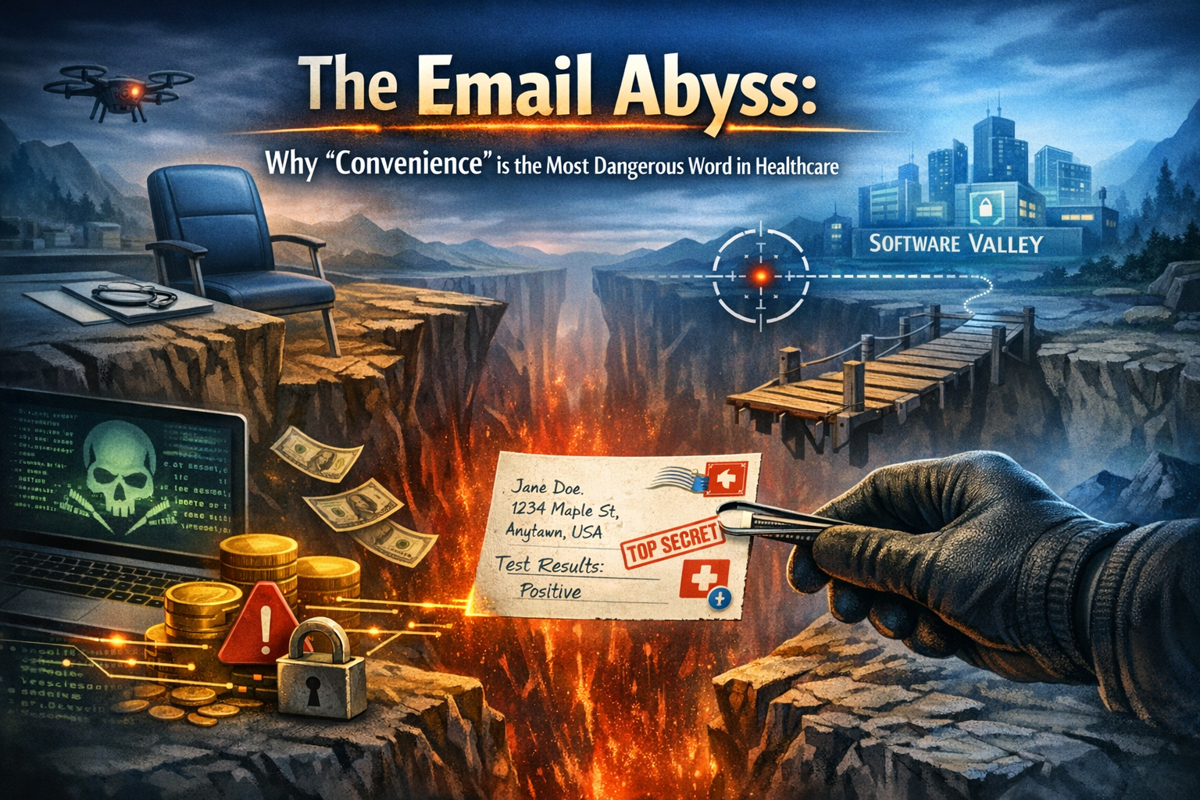
In our journey through Software Valley, there is a tempting shortcut that almost every clinician considers: Standard Email. It’s fast, everyone has it, and it feels "free."
But in 2026, this shortcut has become a dangerous abyss. As cyber-attacks grow more sophisticated, the gap between "sending a quick message" and "triggering a massive data breach" has never been smaller.
1. The Technical Reality of the "Abyss"
Standard email (like a basic @gmail.com or @yahoo.com account) was never designed to carry Protected Health Information (PHI). Here is why it fails the security test:
· The "Man-in-the-Middle": Unencrypted emails are like postcards; they can be read by anyone handling them as they travel across the internet. In 2026, "Adversary-in-the-Middle" attacks use AI to intercept these "postcards" in real-time.
· The Authentication Gap: Without Multi-Factor Authentication (MFA) and strict sender verification (like DMARC), it is incredibly easy for hackers to "spoof" your clinic's email address, leading to devastating phishing attacks on your patients.
· The Ghost of Deleted Data: Even if you delete an email, copies often live forever on unmanaged servers or in the recipient's "Sent" folder, creating a permanent, un-auditable trail of PHI.
2. The Legal Chasm: No BAA, No Compliance
Under modern regulations like HIPAA, the GDPR, and Zimbabwe’s Data Protection Act, you are legally responsible for every vendor that touches your patient data.
· The BAA Requirement: If you use an email provider for clinical work, you must have a signed Business Associate Agreement (BAA). Most free consumer email providers will never sign one.
· The 24-Hour Clock: New 2026 mandates often require business associates to report security incidents within 24 hours. If you are using a standard email provider, you have zero visibility into whether a breach has even occurred.
3. The Human Factor: Autocomplete and Accidents
Technology aside, the biggest risk is often a simple typo.
· The Autocomplete Nightmare: We’ve all done it—typing "John" and accidentally hitting "John B." instead of "John A." In a clinical setting, that "Reply-All" or autocomplete mistake is a reportable HIPAA breach.
· The Loss of Trust: 60% of healthcare organizations reported an email-related security incident last year. For a patient, receiving their sensitive test results in an unencrypted email isn't just a "tech issue"—it's a sign that the clinic doesn't value their privacy.
4. Crossing the Abyss with Flaura
At Flaura, we believe you shouldn't have to choose between convenience and security. Instead of forcing you into the Email Abyss, we provide a Secure Portal Pathway:
· Zero-Knowledge Encryption: Messages are encrypted at rest and in transit.
· Full Audit Logs: See exactly who accessed a record and when—critical for regulatory compliance and internal peace of mind.
· Identity Verification: Ensuring that the person reading the sensitive information is actually the patient.
Is your clinic still using the "Email Shortcut"? It might feel faster today, but the cost of a single breach in 2026 can exceed $4.7 million in legal fees, fines, and lost reputation.
Don't let your practice fall into the abyss. Read our [Complete Guide to Digital Clinical Communication] to learn how to build a secure, compliant bridge for your patients.